top of page


Phishing Incident Response Playbook: A Complete Guide
A phishing incident response playbook is essential. This guide delivers a comprehensive framework covering detection, investigation, containment, eradication, and recovery—aligned with real-world tools such as Microsoft Sentinel and Microsoft Defender for Office 365.
5 days ago4 min read


Azure Cloud Security Guide: Best Practices, Tools & Defensive Strategies
Azure misconfiguration remains one of the leading causes of cloud breaches. Understanding Azure cloud security best practices is critical.
Mar 13 min read


Cyber Essentials Made Simple: A Practical Guide for UK Businesses
What Cyber Essentials is.
Why it matters.
What’s actually assessed.
And provide a practical Cyber Essentials checklist you can use today.
Jan 214 min read


KQL in SecOps (3) – Aggregation & Summarization
Detect patterns over time, Identify anomalies and outliers, Build actionable alerts, Generate SOC metrics for dashboards
Jan 164 min read

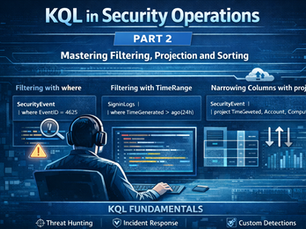
KQL in SecOps (2) - Mastering Filtering, Projection, and Sorting
The fundamentals of querying data—filtering logs, selecting the right fields, and sorting results.
Jan 54 min read


KQL in SecOps (1) - Why Every Security Analyst Must Learn KQL
What KQL is, Why it is critical for SOCs, How analysts use it daily, Common misconceptions and best practices.
Dec 22, 20256 min read


AI Prompt Injection Explained: Risks, Attack Examples & 7 Defense Methods
AI Prompt Injection Explained: Risks, Attack Examples & 7 Defense Methods
Dec 13, 20254 min read


AI and Cybersecurity: Transforming the Landscape in 2026
Explore how AI empowers both sides of the security equation, the emerging purple team collaborations that unite them, and the governance needed to keep innovation secure.
Nov 8, 20254 min read


Google Dorks - Advanced Search
Explore what Google dorks are, how to use them effectively, and provide real-world examples for practical use.
Oct 14, 20253 min read
bottom of page

